The Domain Controller (DC)
Identity Security: Active Directory Fundamentals & Attack Surface
1. The Logical Structure: Organizing the Kingdom
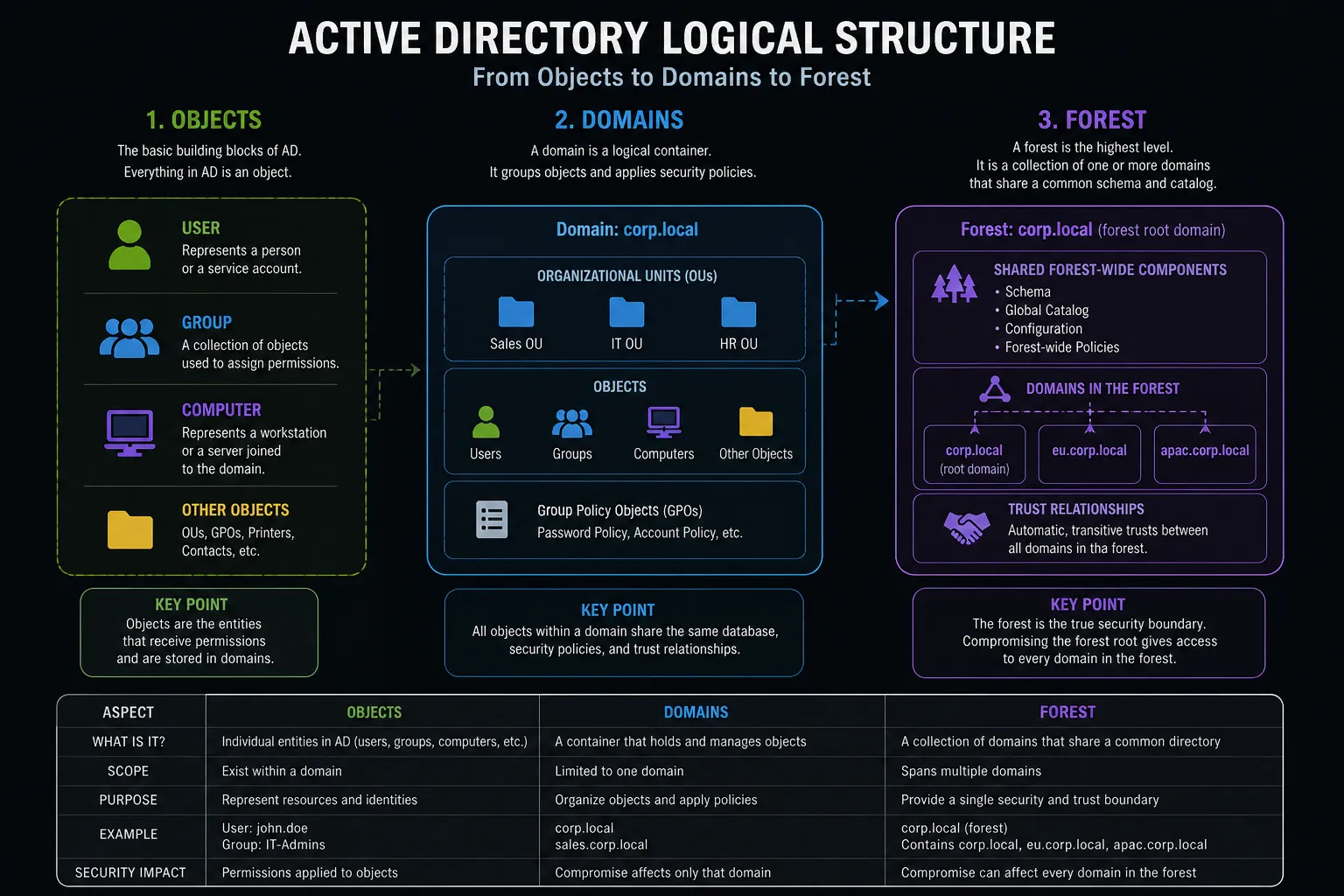
Section titled “1. The Logical Structure: Organizing the Kingdom”The logical architecture of AD is a hierarchical framework of objects. Threat actors navigate this hierarchy to escalate privileges and establish persistence.
A. The Object (The Basic Unit)
Section titled “A. The Object (The Basic Unit)”Everything within AD is an object—a directory entry containing a specific set of attributes.
- User: Represents a human identity or a service account. Targeted for Credential Attacks.
- Group: A container for other objects, simplifying permission assignments.
- Computer: Represents a workstation or server joined to the domain.
B. The Domain
Section titled “B. The Domain”A Domain is a logical grouping of objects that share the same directory database and security policies. It is identified by a DNS name (e.g., corp.local).
While often considered a security boundary, a domain is merely an administrative boundary within a larger context. If an attacker compromises a Domain Admin account, they control every object within that specific domain, but their reach may extend further depending on trust relationships.
C. The Forest (The True Security Boundary)
Section titled “C. The Forest (The True Security Boundary)”A Forest is the highest-level container in Active Directory. It is a collection of one or more domains that share an automatic, transitive trust relationship, a common schema, and a global catalog.
D. The Organizational Unit (OU)
Section titled “D. The Organizational Unit (OU)”An OU is a sub-container within a domain used to organize objects hierarchically. Its primary security purposes are delegation of administration (e.g., allowing local IT to reset passwords only for the “Sales” OU) and the targeted application of Group Policy Objects (GPOs). Attackers often hunt for misconfigured OUs where they possess unexpected write privileges.
2. The Physical Structure: Powering the Kingdom
Section titled “2. The Physical Structure: Powering the Kingdom”The physical structure dictates how AD data is hosted and replicated across the network.
The Global Catalog (GC)
A partial, read-only index of all objects across all domains in the forest. It allows users and applications to quickly search for objects forest-wide without querying each domain individually. It is heavily utilized during the logon process.
3. Tier 0 Security and Vigilance
Section titled “3. Tier 0 Security and Vigilance”Active Directory security relies on the concept of Tiering, where Domain Controllers represent the apex: Tier 0.
The Single Role Principle
Section titled “The Single Role Principle”A Domain Controller must be treated as a highly classified sanctuary. To minimize its attack surface, a DC should have NO other roles installed besides Active Directory Domain Services (AD DS) and DNS. Every additional software or service installed on a DC introduces potential vulnerabilities that could compromise the entire network’s root of trust.
The DC-DHCP Vulnerability (A Classic Misconfiguration)
Section titled “The DC-DHCP Vulnerability (A Classic Misconfiguration)”- The Flaw: Installing the DHCP server role (which distributes IP addresses) directly on a Domain Controller is a common, historically disastrous bad practice.
- The Risk: The DHCP service executes with high privileges. Historically, severe vulnerabilities have allowed remote attackers to exploit the DHCP service to execute arbitrary code. If that service runs on a DC, the attacker bypasses lateral movement entirely and achieves immediate domain dominance. Furthermore, malicious DHCP configurations can be abused to poison DNS records dynamically.
- The Rule: A DC is a directory service. Nothing else. No DHCP, no print spooler, no file sharing, no web servers.
4. DFIR Perspective: Understanding the Attack Path
Section titled “4. DFIR Perspective: Understanding the Attack Path”Understanding these fundamental building blocks is mandatory for contextualizing a cyberattack.
- Identifying the Crown Jewels: Domain Controllers are the critical assets. Any suspicious activity originating from or targeting a DC (such as unexpected Event 4688 processes or unauthorized Object Access) is a maximum-priority alert.
- Calculating the “Blast Radius”:
- If a standard Domain Admin is compromised, the specific domain is lost.
- If an Enterprise Admin (or the
krbtgtaccount of the root domain) is compromised, the entire forest is lost, allowing attackers to forge cross-domain Golden Tickets.
- Tracing the Kill Chain: Attackers rarely land directly on a DC. They follow a structured path:
- Initial access via a standard user.
- Lateral Movement to compromise a workstation administrator.
- Privilege escalation to compromise a server hosting sensitive sessions.
- Final execution of Persistence & Domination techniques (like DCSync) against the Domain Controller itself.
References & Further Reading
Section titled “References & Further Reading”- Microsoft Learn: Active Directory Domain Services Overview
- Related Playbook: AD Credential & Password Attacks
- Related Playbook: AD Lateral Movement Techniques
- Related Playbook: AD Persistence & Domination (DCSync, Golden Ticket)